On Tuesday, November 1 2022 between 1300-1700 UTC, the OpenSSL project announced the release of a new version of OpenSSL (version 3.0.7) that will patch a critical vulnerability in OpenSSL version 3.0 and above. Only OpenSSL versions between 3.0 and 3.0.6 are affected at the time of writing. At this moment the details of this vulnerability are not yet disclosed, only that it is rated as critical (CVSS v3.0 Rating 9.0-10.0) and the affected versions. Due to the high CVSS score, which is not easily assigned to a CVE, it is very possible that the vulnerability is remote exploitable with a low attack complexity and a high impact. OpenSSL describes a critical vulnerability as follows:
CRITICAL Severity. This affects common configurations which are also likely to be exploitable. Examples include significant disclosure of the contents of server memory (potentially revealing user details), vulnerabilities which can be easily exploited remotely to compromise server private keys or where remote code execution is considered likely in common situations. These issues will be kept private and will trigger a new release of all supported versions. We will attempt to address these as soon as possible.
https://www.openssl.org/policies/general/security-policy.html
The last critical vulnerability affecting the OpenSSL cryptographic software library was the well-known Heartbleed bug which was disclosed in 2014 (CVE-2014-0160). The Heartbleed vulnerability affected many systems and even 5 years after the vulnerability was discovered, many systems were still unpatched. The Heartbleed bug allows attackers to read the memory of systems that implement vulnerable versions of the OpenSSL software (from OpenSSL 1.0.1 to 1.0.1f).
It is important to note that the vulnerability only affects OpenSSL version 3.0 and higher, versions before 3.0 are not vulnerable. Version 3.0 of OpenSSL was released in September 2021 and for this reason is not yet as widely distributed as previous versions (such as the 1.1.x branch). Nevertheless, starting next Tuesday, vendors using OpenSSL 3.0 in their software will be working hard to make patches available to patch the OpenSSL vulnerability. From the moment patches are available, it is important that they are also applied consistently by system owners. Another difficulty with high impact vulnerabilities is how vendors deal with end-of-life products that use vulnerable implementations of the software. In the case of this vulnerability, this is expected to be somewhat limited as OpenSSL 3.0 was released recently and many systems still use older OpenSSL versions.
Affected Products
At the moment we know that the following systems use OpenSSL 3.0 and higher:
- CentOS Stream 9
- Fedora 36, 37 & Fedora Rawhide (current development version of Fedora Linux)
- Kali Linux 2022.3
- Linux Mint 21 Vanessa
- Redhat ES 9
- Ubuntu 22.04
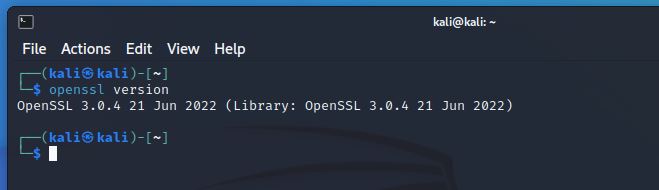
When OpenSSL is installed on a system you can check the system version with the following command:
openssl version
As we can see on the (incomplete) list of affected systems it really concerns the most recent versions of operating systems. Operating system versions before September 2021 use OpenSSL 1.1.1 which is not affected. MacOS is also not affected as it uses LibreSSL by default and not OpenSSL, unless OpenSSL has been installed afterwards of course.
Furthermore, it is important to note that this list only includes operating systems. Many software vendors integrate OpenSSL in their products, think of web- and e-mail server software such as Apache and Nginx. Firewall solutions and network appliances from vendors such as Juniper, Fortinet, Cisco which also need to be patched if they are using one of the affected OpenSSL versions.
The fact is that we don’t know any more about the OpenSSL vulnerability at this point and we’ll have to wait until Tuesday for more information to really assess the impact of the bug.
Update November 1, 2022 18:00
- The OpenSSL team just released OpenSSL 3.0.7.
- The OpenSSL Project disclosed two vulnerabilities CVE-2022-3602 (Remote Code Execution) and CVE-2022-3786 (Denial of Service).
- CVE-2022-3602 is an arbitrary 4-byte stack buffer overflow that could trigger crashes or result in remote code execution (RCE).
- CVE-2022-3786 can be exploited by attackers via malicious email addresses to trigger a denial-of-service state via a buffer overflow.
- This occurs after certificate chain signature verification and requires either a CA to have signed the malicious certificate or for the application to continue certificate verification despite failure to construct a path to a trusted issuer.
- Pre-announcements rated the vulnerability as CRITICAL, further analysis downgraded it to HIGH.
- Users are still encouraged to upgrade to a new version as soon as possible.
- The bug is fixed here: https://github.com/openssl/openssl/commit/fe3b639dc19b325846f4f6801f2f4604f56e3de3
- More information is available here: https://www.openssl.org/news/vulnerabilities.html#CVE-2022-3602 & https://www.openssl.org/news/secadv/20221101.txt
- The OpenSSL team is not aware of any working exploit that could lead to remote code execution.
“We still consider these issues to be serious vulnerabilities and affected users are encouraged to upgrade as soon as possible”
https://www.openssl.org/blog/blog/2022/11/01/email-address-overflows/
The OpenSSL team lead
Bug Bounty – An Advanced Guide to Finding Good Bugs
Real World Bug Bounty Techniques

Website Hacking / Penetration Testing & Bug Bounty Hunting
Become a bug bounty hunter! Hack websites & web applications like black hat hackers and secure them like experts.



















