In this tutorial we will be using a Nmap script to scan a target host for SMB vulnerabilities. SMB stands for Server Message Block and does not have a great reputation when it comes the security and vulnerabilities. SMB1 was used in Windows 2000 and Windows XP which allowed null sessions which could be used to retrieve a great deal of information about the target machine. Later versions of SMB were also subject to many vulnerabilities which allowed anything from remote code execution to stealing user credentials. For this reason every penetration test should be checking for SMB vulnerabilities.
We will be using NMap scripts to scan a target host for SMB vulnerabilities. The Nmap Scripting Engine (NSE) is on of Nmap’s most powerful and flexible features. With the latest version, nmap 7.0 the scripting engine has been greatly expanded, Nmap 7 contains more than 170 new scripts. Let’s continue this tutorial with scanning for SMB vulnerabilities with Nmap: The frontpage on Samba.org describes Samba as:
Since 1992, Samba has provided secure, stable and fast file and print services for all clients using the SMB/CIFS protocol, such as all versions of DOS and Windows, OS/2, Linux and many others. Samba is an important component to seamlessly integrate Linux/Unix Servers and Desktops into Active Directory environments. It can function both as a domain controller or as a regular domain member.
Scanning from SMB vulnerabilities
The following command executes Nmap with a script:
nmap –script [scriptname]-p [port][host]
If nmap returns an error try to add –script-args=unsafe=1 so we get the status for SMB vulnerabilities:
nmap –script [scriptname]–script-args=unsafe=1 -p [port][host]
To have Nmap scan a target host for SMB vulnerabilities, use the following command:
nmap –script smb-check-vulns.nse –script-args=unsafe=1 -p445 [host]
The following command enumerates the SMB shares on a target host:
nmap –script smb-enum-shares.nse –script-args=unsafe=1 -p445 [host]
There is also a script for OS discovery which uses SMB:
nmap –script smb-os-discovery.nse –script-args=unsafe=1 -p445 [host]
Use the following command to enumerate the users on a target host:
nmap –script smb-enum-users.nse –script-args=unsafe=1 -p445 [host]
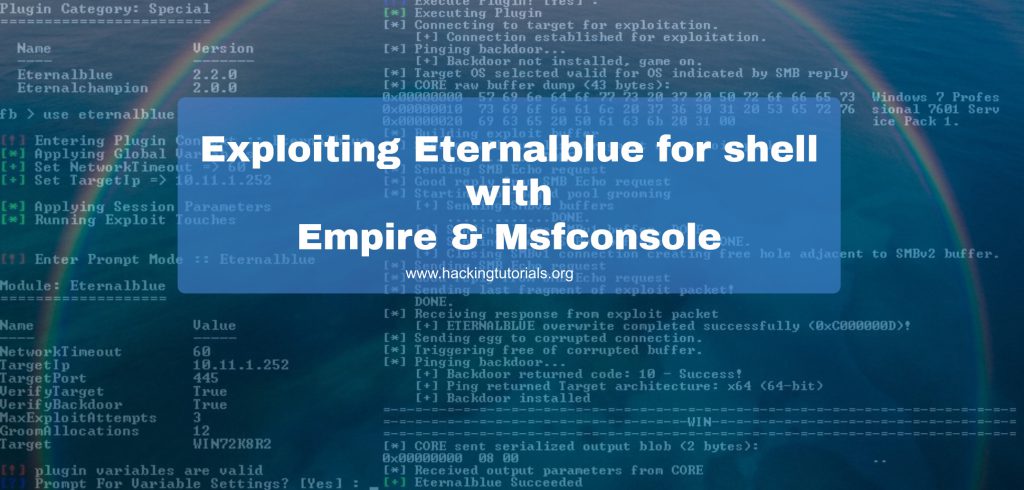
Scanning a host for MS17-010 Eternalblue with Nmap
You can also use Nmap to scan a target, or a range of targets, for MS17-010. Before we can run this scan we need to download the “smb-vuln-ms12-010.nse” script first from the link below:
https://raw.githubusercontent.com/cldrn/nmap-nse-scripts/master/scripts/smb-vuln-ms17-010.nse
Store the file in the Nmap scripts directory and then launch the scan as shown below:
nmap -p 445 -script=smb-vuln-ms17-010.nse [host]
The following command targets a range of hosts in your network:
nmap -p 445 -script=smb-vuln-ms17-010.nse [host-range]
SMB Vulnerabilities Video Tutorial
Thanks for watching and please subscribe to my YouTube channel 🙂
Related Nmap Y3llowl4bs
Open Port Scanning and OS Detection with Nmap in Kali Linux
Scanning a network for live hosts with Nmap
How to enumerate webserver directories with Nmap
Scanning for SMB vulnerabilities using Nmap
Heartbleed SSL bug Scanning using Nmap on Kali Linux
Check out these SMB related hacking tutorials too:
Hacking Courses on Udemy
Bug Bounty – An Advanced Guide to Finding Good Bugs
Real World Bug Bounty Techniques

Website Hacking / Penetration Testing & Bug Bounty Hunting
Become a bug bounty hunter! Hack websites & web applications like black hat hackers and secure them like experts.



















